WDS Client Naming Policy ignored when deploying Windows 7
If you find that your client naming policy as set on your Windows Deployment Services server is being ignored when you deploy a Windows 7 image, you may find that there’s a little known setting which has not been enabled in the ImageUnattend.xml file associated with the image you are deploying.
This post on Microsoft’s answers website discusses the issue at length with many people falling foul of the problem. An answer is given at the very end but the reasons for the answer are not clearly explained.
The setting and the reasons why you might choose either option is explained more clearly in the Technet documentation for Windows Deployment Services.
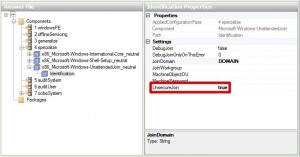
To summarise, if you are performing automated domain join operations for a Windows 7 image and find that your Client Naming Policy is being ignored, you should enable the UnsecureJoin option for the specialize phase of the x86_Microsoft-Windows-UnattendedJoin_neutral component as in the following screenshot:
 Some of you may be concerned that the UnsecureJoin feature would actually reduce security on your domain and for those of you with pure Windows Server 2008R2 domains, you may need to dial down security and alter the Default Domain Controllers Policy to Allow cryptography algorithms compatible with Windows NT 4.0 before you are able to add computers to the domain using the UnsecureJoin feature. If you are still deploying Windows XP clients on to your network, you’ll find you must do this when you specify DoOldStyleDomainJoin in the sysprep.inf file.
Some of you may be concerned that the UnsecureJoin feature would actually reduce security on your domain and for those of you with pure Windows Server 2008R2 domains, you may need to dial down security and alter the Default Domain Controllers Policy to Allow cryptography algorithms compatible with Windows NT 4.0 before you are able to add computers to the domain using the UnsecureJoin feature. If you are still deploying Windows XP clients on to your network, you’ll find you must do this when you specify DoOldStyleDomainJoin in the sysprep.inf file.
The biggest disadvantage of doing a secured domain join is that the credentials are stored unsecured in the ImageUnattend.xml file which any nosey parker on your network could discover if they poke around any shares on your WDS server so my recommendation is to use UnsecureJoin wherever possible to avoid this security issue.
-Lewis






Thanks a lot. This saved me a lot. I had everything works perfectly except the naming policy. Now after I enabled the unsecured join it worked like charm.